The key risks and how enterprises can avoid them
Enterprise mobility IT security is often likened to insurance. Something you account for simply because you have to have it. However, this limited view misses the point. Security provides more than just cover in response to a specific event. It can provide assurance too – allowing your enterprise to operate and innovate without the risk of data breaches.
No one-size-fits all approach
There remains some difference of opinion over the value of security. What everyone can agree on is that it is a complex subject that touches many areas of the organisation. When you consider the variety of mobility use cases, application methodologies and deployment options of individual enterprises, the overall value of security, as well as the complexity, becomes more evident.
In a retail store, staff with tablets can serve customers quickly. But those customers want assurances that the personal information they hand over is safe on these devices. In manufacturing, there is the rise of wearable technologies to consider. This change will mean securing the flow of data from a large number of end points.
Application methodologies also vary depending on the use case and the type of device. From web-based apps through to native mobile apps or even hybrids, each instance places unique security demands on the enterprise.
The mobile deployment options available can add another level of complexity. If the enterprise encourages Bring Your Own Device (BYOD) or uses consumer-grade technology then the IT team might have to commit additional resources. They will have to develop in-house security solutions when consumer-grade mobile operating systems (OS) do not provide the required levels of security. There are also additional concerns when it comes to protecting network activity and security for WAN or WLAN connectivity.
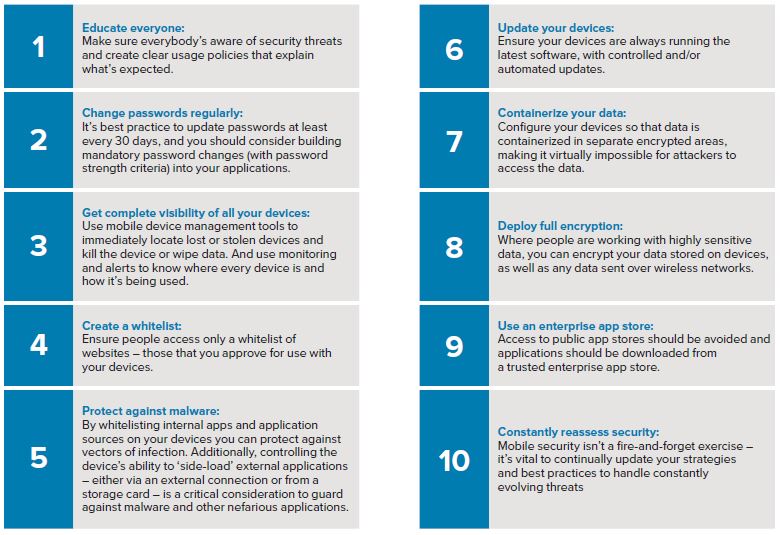
A useful checklist
Contact Skywire to discuss your OS security options today



Comments are closed.